Critical remote vulnerability in Nginx CVE-2026-9256
Let’s rebuild Nginx with CVE-2026-9256 patch according to the Debian-way.
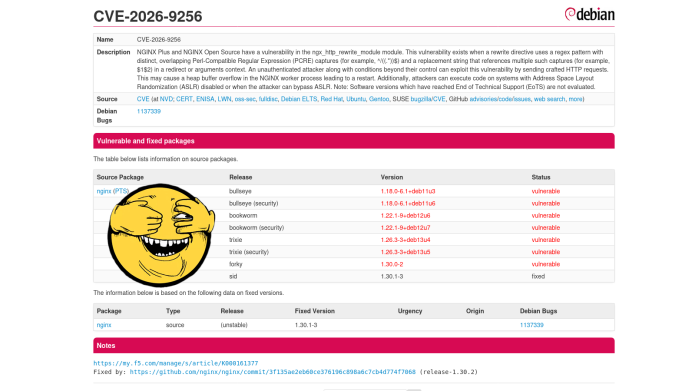
A critical vulnerability in nginx allows remote code execution with the privileges of the nginx worker process by sending a specially crafted HTTP request.
But that’s not the point.
The problem is that Debian maintainers are in no hurry to release a new patch package.
1 2 3 4 5 | apt --no-install-recommends \ --no-install-suggests install \ build-essential \ fakeroot \ devscripts |
nano /etc/apt/sources.list
1 2 3 4 | # trixie sources
deb-src https://deb.debian.org/debian/ trixie main contrib non-free non-free-firmware
deb-src http://security.debian.org/debian-security/ trixie-security main contrib non-free non-free-firmware
deb-src https://deb.debian.org/debian/ trixie-updates main contrib non-free non-free-firmware
|